Is it good practice to set Samba's "server min protocol" to deny SMBv1-requests?
I have a fairly small home network, consisting of:
- a NAS (running OpenMediaVault), NetBIOS-Name
FooBarNAS - a Raspberry Pi 2 with dnsmasq to provide DHCP/DNS services around the place,
- a modem (with deactivated DHCP, obviously),
- multiple clients running Windows >= 7 & some clients running linux variants
As far as I understand, my network is not accessible (i.e. $ ping my.modem's.ip.adress will fail) via the Internet.
About a year ago, I noticed that many websites, including Microsoft's TechNet-blog and US-CERT, started to convince people to stop using SMBv1 on their servers (and clients).
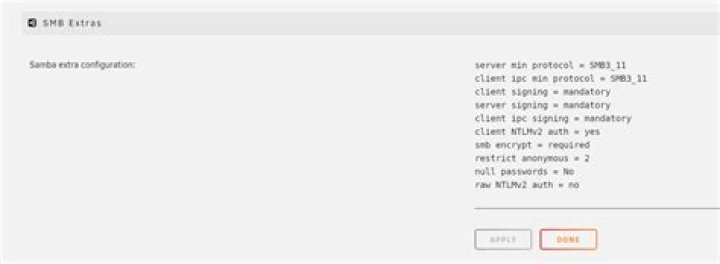
Although I do not think that I have to cease using SMBv1 at all costs in my local network, I thought that it might be a good idea to give it a go, anyway. So in my NAS's smb.conf, I added client min protocol = SMB2_10 and server min protocol = SMB2_10 (SMBv2.1 was introduced with Windows 7, and since I do not own any devices with Windows versions below that, I thought that this would be a good start).
However, once I add this lines and restart samba, my computers cannot find the NAS anymore in the Explorer's "Network"-section, although I can still access it by typing \\FooBarNAS in the adress-bar (or using its IP-address). If I delete the lines again (and restart), FooBarNAS appears again.
I tried to add netbios name = FooBarNAS in smb.conf, but that did not change the behavior, either.
As this behavior is annoying (especially for those people in the house who do not like to use the address bar), and I am unable find any definitive information towards the topic in the Internet, my question is:
In home networks, is the security increased by "switching off" SMBv1 in Samba?
2 Answers
The issue here is very simple, Network browsing is using SMBv1!!! In the latest SNIA SDC Microsoft announced about the death of SMBv1(disable by default - register) but still the network browsing will work over SMBv1.
That is why you could not see your device.
Try to modify only the server : server min protocol = SMB2_10And leave the Client to support SMBv1
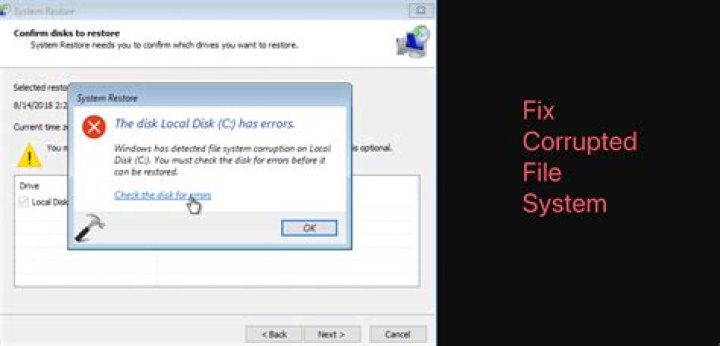
Run secpol.msc
I had to disable this here to get mine to work.
3