Bad system call (core dumped) /usr/share/man/man1
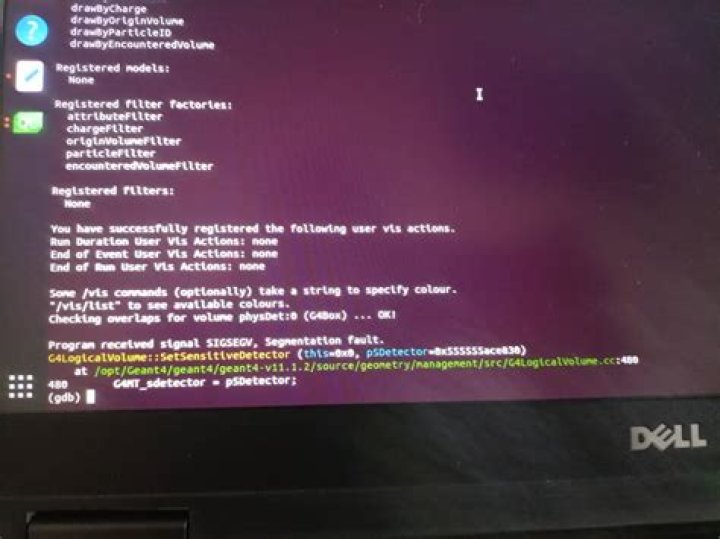
I am running on Ubuntu 18.04.1 release 4.15.0-38-generic.
I know this or a similar question was asked a few months ago and there seemed to be a fix or a workaround in progress.
dpkg --list man-db
Desired=Unknown/Install/Remove/Purge/Hold
| Status=Not/Inst/Conf-files/Unpacked/halF-conf/Half-inst/trig-aWait/Trig-pend
|/ Err?=(none)/Reinst-required (Status,Err: uppercase=bad)
||/ Name Version Architecture Description
+++-==============-============-============-=================================
iF man-db 2.8.3-2ubunt amd64 on-line manual pagerEvery time I run Software Updater or try to install a new package it takes forever, and the reason seems to be lots of core dumps. Here is a small sample:
>
usr/bin/mandb: zcat: Bad system call (core dumped)
/usr/bin/mandb: zcat < /usr/share/man/man1/pbmtomda.1.gz: Bad system call (core dumped)
/usr/bin/mandb: /usr/lib/man-db/manconv -f UTF-8:ISO-8859-1 -t UTF-8//IGNORE -q: Bad system call (core dumped)
/usr/bin/mandb: zcat < /usr/share/man/man1/pamfile.1.gz: Bad system call (core dumped)
/usr/bin/mandb: zcat: Bad system call (core dumped)
/usr/bin/mandb: zcat < /usr/share/man/man1/pamfile.1.gz: Bad system call (core dumped)
/usr/bin/mandb: /usr/lib/man-db/manconv -f UTF-8:ISO-8859-1 -t UTF-8//IGNORE -q: Bad system call (core dumped)
/usr/bin/mandb: zcat < /usr/share/man/man1/pnmtorast.1.gz: Bad system call (core dumped)
/usr/bin/mandb: zcat: Bad system call (core dumped)
/usr/bin/mandb: zcat < /usr/share/man/man1/pnmtorast.1.gz: Bad system call (core dumped)
/usr/bin/mandb: /usr/lib/man-db/manconv -f UTF-8:ISO-8859-1 -t UTF-8//IGNORE -q: Bad system call (core dumped)
I believe AppArmor was identified as a possible culprit by someone at Astrill but I am not using any package called Astrill VPN. I have Expressvpn, the Ubuntu network managers, pptp-linux and openvpn.
I have tried reinstalling man-db and apparmor but nothing changes.
I am now on Ubuntu 19.4 and still getting these mandb error messages. Every software install or update takes ages because it gets to about 89% then starts looping through these error messages. I had hoped that waiting for a new release might eventually solve this on its own, but it seems not. Any clues on what is going on and assistance to fix this would be appreciated.
(The above edit was made by me but I wasn't signed in!)
1 Answer
Thanks for the debugging information by email.
This turns out to be the fault of ESET File Security. I've applied workarounds for this program in the past, but apparently I needed to do a bit more.
Briefly, this is an anti-malware tool that injects code into every process that involves sending a message to a separate program on your machine any time certain events happen. Now, man-db has its own security measures that are intended to defend against malicious documents somehow managing to exploit bugs in the tools that process them, and those involve restricting the system calls that those tools can make to only those that they're supposed to need in order to do text processing. Unfortunately, what ESET is doing is quite hard to distinguish from what malware might decide to do, so these two security measures fight with each other.
My reluctant compromise (although ultimately I'd like to figure out something better) has been to detect when ESET is installed and allow a few more system calls in that case, but this is a difficult exercise and it's easy to miss some. I've committed a change to add another one to that list in response to your trace. This will need to be backported to stable Ubuntu releases before you see the benefit of it, and due to other commitments I won't have time to start that process until at least the middle of next week. In the meantime, you have a couple of options to get past this problem:
- Uninstall ESET File Security (temporarily or otherwise).
- Set the environment variable
MAN_DISABLE_SECCOMP=1. This is a bit difficult to do persistently via graphical tools such as Software Updater, but if you're willing to useaptfrom a terminal then you can just remember to runsudo MAN_DISABLE_SECCOMP=1 apt full-upgradeorsudo MAN_DISABLE_SECCOMP=1 apt install some-packageor whatever.
I'll update this answer once packages including my change are available. (Unfortunately I have no good way to confirm that this is fixed all the way, so it's possible this will be a whack-a-mole exercise where we have to go round again.)
5